Instant and automatic data logging has long become the new norm. It is applicable everywhere from the sites that you browse to any corporate system that you have adopted in your company. All the Whos, Whens and Wheres are logged automatically to provide uncompromised data.
No wonder that our partners and their clients requested to integrate this tool to their monitoring solutions as well - and here it is. Now let’s see what this feature is about.
User actions monitoring
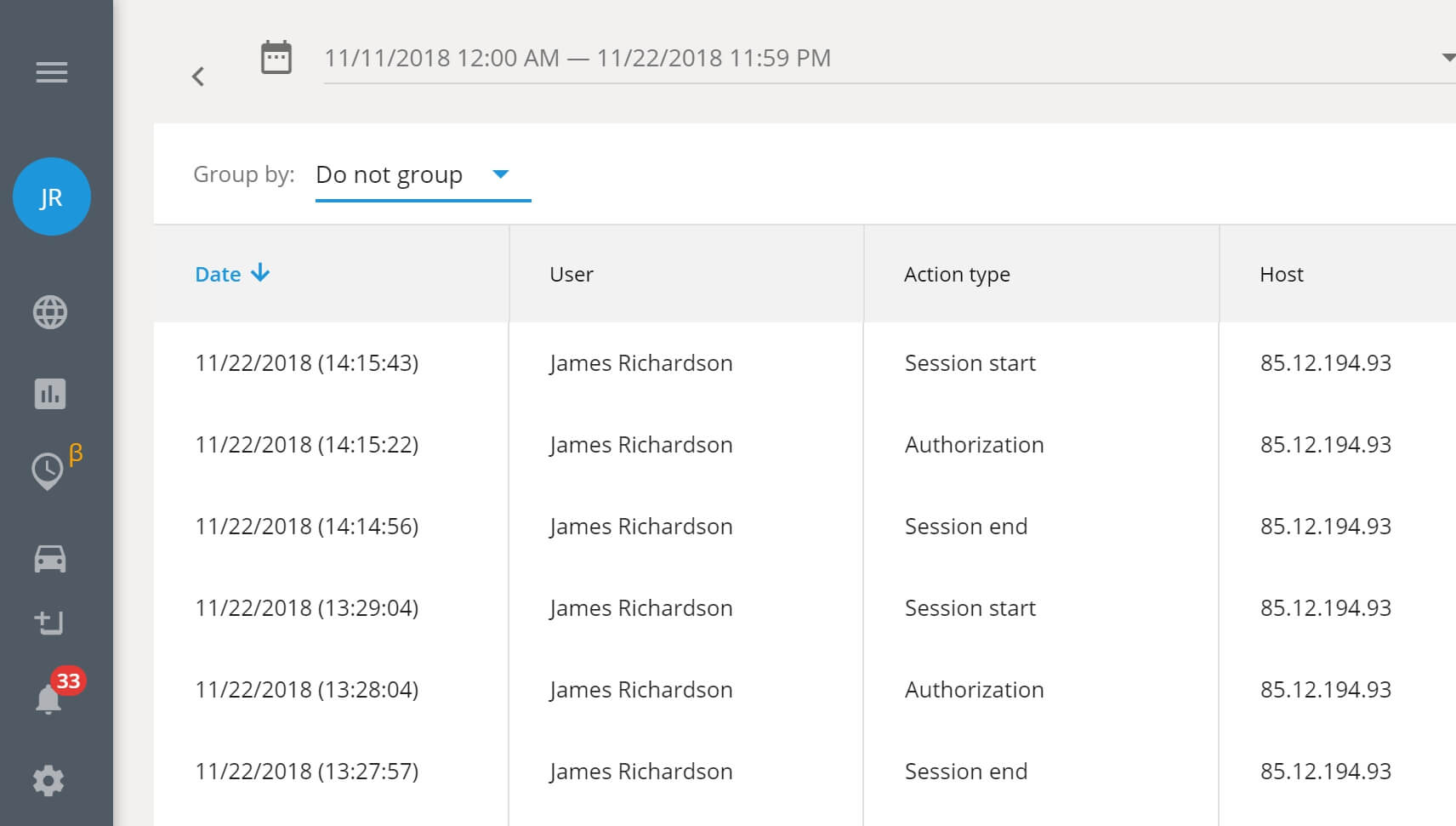
Before anything else, Activity log is a tool for monitoring. It is reliable, easy-to-use and automatic. And unbiased: the entries can’t be edited or deleted even by the account owner. Activity log displays the exact date and time an employee (identified by a User name and an IP-address) has interacted with the system. Managers can view the current situation or check data for any past period to define the responsible person and action type on the click.
But it’s not all about Big-Brother(ish) control. Employees and supervisors have their fair share of benefits.
- First of all, Activity log shows the actual working hours from when an employee started using the system to when they logged out.
- Secondly, it builds accountability between the teams: when they know that their actions can always be verified (this very day or months after), the employees become more responsible and work more efficiently.
Renowned standard for fault-free operation
In some companies, however, Activity log is more than just a nice tool. Recently one of our partners received a request from their client in Eastern Europe, a worldwide logistics and delivery giant DHL. Due to international security requirements they had to implement a solution for daily logging in and logging out operations in their GPS tracking system. Needless to say, we were more than happy to help.
Let’s see the feature in operation.
It shows Date, User name, Action type, and the IP-address of a user. For your convenience any data can be grouped and filtered by date, by action type or by employees.
Unlimited customer-driven potential
Probably the best thing about this feature is its limitless growth potential. For now we have introduced the most requested and the most essential parameters: authorization, session start, session end, and login from the owner’s account. But there can be more! A few of our partners have already introduced this feature to their clients and received a great deal of positive feedback. The most frequently asked question in this regard however is...‘what’s next’.
Well, the next portion will entirely depend on the customers’ requests. That’s the reason why we introduced this feature in the first place. Based on popular demand we guess that the new addition to the action types will concern geofencing and POIs: who it was created, edited or deleted by and when. But it’s only one of many possible scenarios.
So make sure you offer this feature to your clients and provide a most accurate feedback. Share your Navixy experience and insights at [email protected].